Offensive Security · AI Security Advisory · Adversarial Emulation
Innovation with Integrity.
Security at the Core.
We break your systems before adversaries do, assess your AI risk before it's exploited, and map your compliance posture before the auditor does. Actual operators. One team.
Get a Free AI Risk Assessment

Validated by the industry
Secure Your Systems. Transform with AI. Trust One Team.
We break your systems to make them unshakeable, then build your AI to make them unstoppable. Secure testing meets intelligent implementation. Two specialties. Zero compromises.
How to measure AI security reliability?
Offensive & Defensive Security
Unified strategies to predict, prevent, and pivot against complex cyber threats before they impact your operations.
Penetration testing
Don’t wait for a breach to find out you’re vulnerable. We simulate a real-world attack to find your flaws and show you exactly how to fix them.
Stay Compliant
Stop worrying about audits. We handle the complex rules and paperwork for you, making sure your business stays compliant and your customers stay happy.
The AI Sword
Stop the guesswork. Start scaling with smarter systems.
Executive AI Co-Pilot
Stop guessing. Build a custom, future-proof blueprint to outpace your competition.
Seamless AI Deployment
Turn your existing tools into an automated powerhouse without the technical headache.
AI Opportunity Audits
Identify exactly where AI will save you 20+ hours a week before you spend a dime.
Innovation Without the Risk
Most companies force you to choose: innovate fast or stay secure. We don't believe in trade-offs. We build your AI future on a rock-solid foundation of offensive security, so you can lead your industry without looking over your shoulder.

Why Suzu Labs
Innovation Without the Risk, and the receipts to prove it.
Every engagement runs as a sequence of named adversary operations, each modeled on a threat actor active against your industry.
Operators, not consultants.
Our team has been on the other side; red teamers, threat intelligence analysts, and practitioners who have done this work, not just advised on it.
CAO — launched April 2026
Launched April 2026, we now offer continuous adversarial emulation as a subscription. Your threat posture improves every month, not just after an annual pen test.
4 Global InfoSec Awards, 2026.
Recognized by peer review across offensive security, AI security, and threat intelligence categories at RSA Conference.
AI and security under one roof.
The same team that assesses your AI risk can red-team your infrastructure and map your compliance gaps. No handoffs. No siloed advisory.
We find what adversaries would find.
Scoped engagement. Agreed threat actor profiles. Attack simulation against your actual environment. You get an executive brief and a technical remediation report with CVSS-scored findings.
We align to your framework.
Whether you're preparing for CMMC, tightening SOC 2 controls, or building against NIST CSF 2.0, we map findings to your specific compliance requirements and prioritize remediation by risk and cost.
We fix it, or we guide you through it.
Retesting included. We don't disappear after the report. CAO clients get continuous simulation so improvements are validated in real time.
Ready to secure what matters?
Most companies choose between speed and safety. We provide both. Schedule a strategy session to see how we stress-test your current infrastructure and build custom, secure AI solutions that scale.
Reserve your briefing
Intelligence from the Field
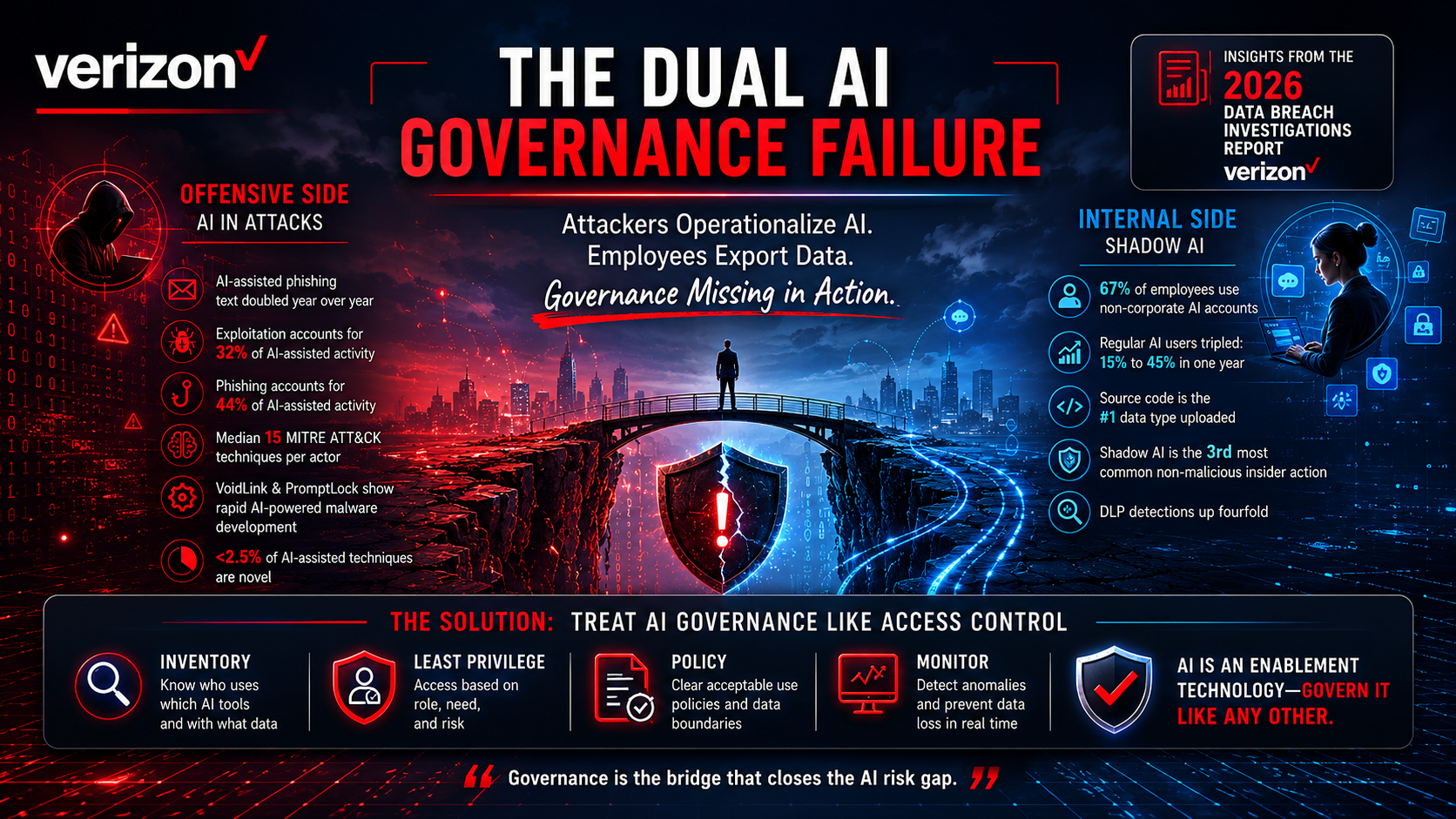
The AI Governance Gap: Verizon's 2026 DBIR Shows Attackers Scaling AI While Employees Leak Data Through It
On May 20, 2026, Verizon published the 2026 Data Breach Investigations Report with a dedicated AI section built on ...

The Remediation Paradox: Verizon's 2026 DBIR Shows Exploitation Winning While Defenders Patch Slower
On May 20, 2026, Verizon published the [2026 Data Breach Investigations ...

The Extension Blind Spot: How One VS Code Plugin Gave Attackers GitHub's Source Code
GitHub's 3,800 Repositories Stolen Through a Single IDE Extension On May 19, 2026, a single VS Code extension on a ...
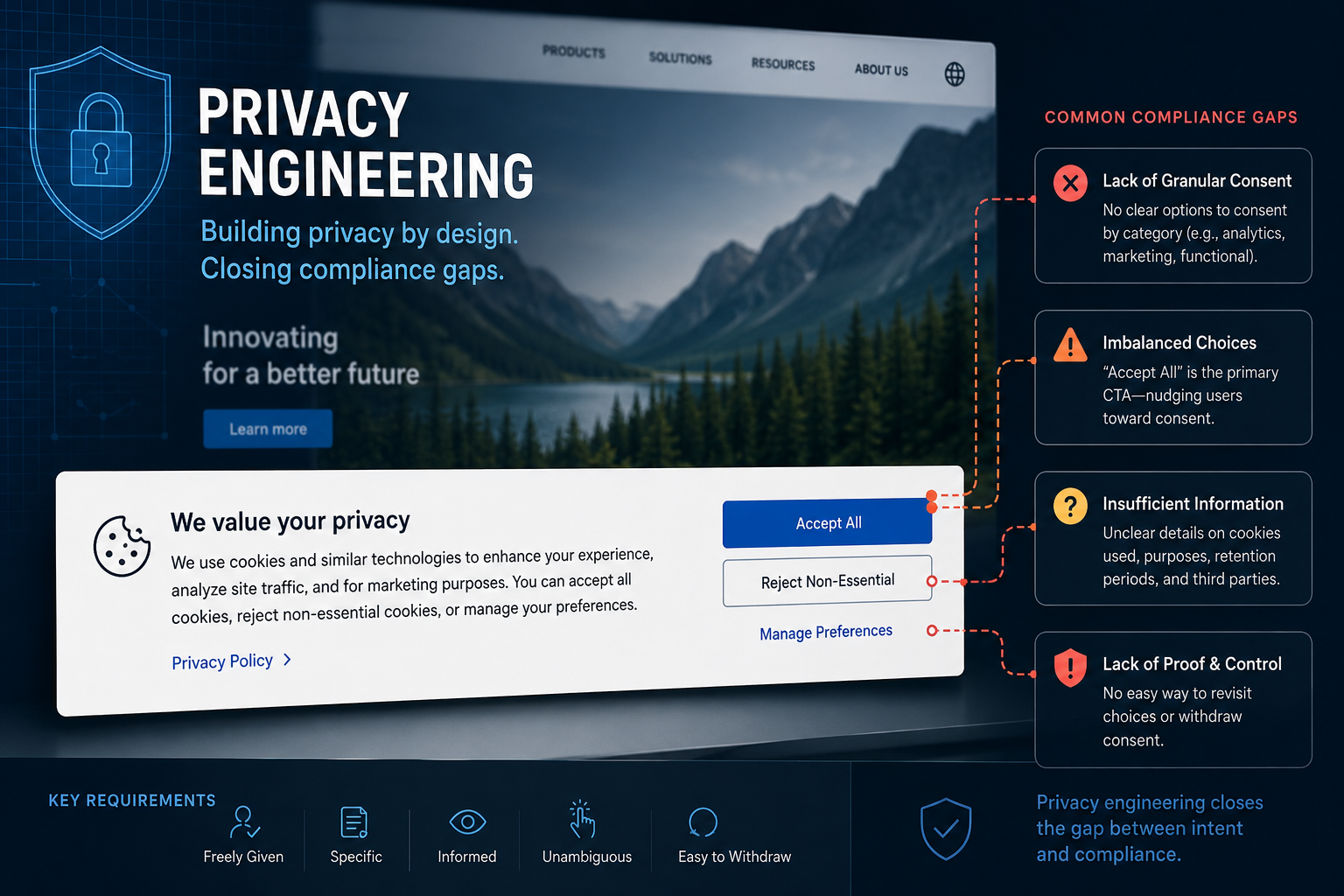
The Cost of a Click: Why Passive Cookie Consent Is Your Biggest Compliance Liability
If you think a basic pop-up banner that reads "By continuing to browse this site, you accept cookies" protects your ...
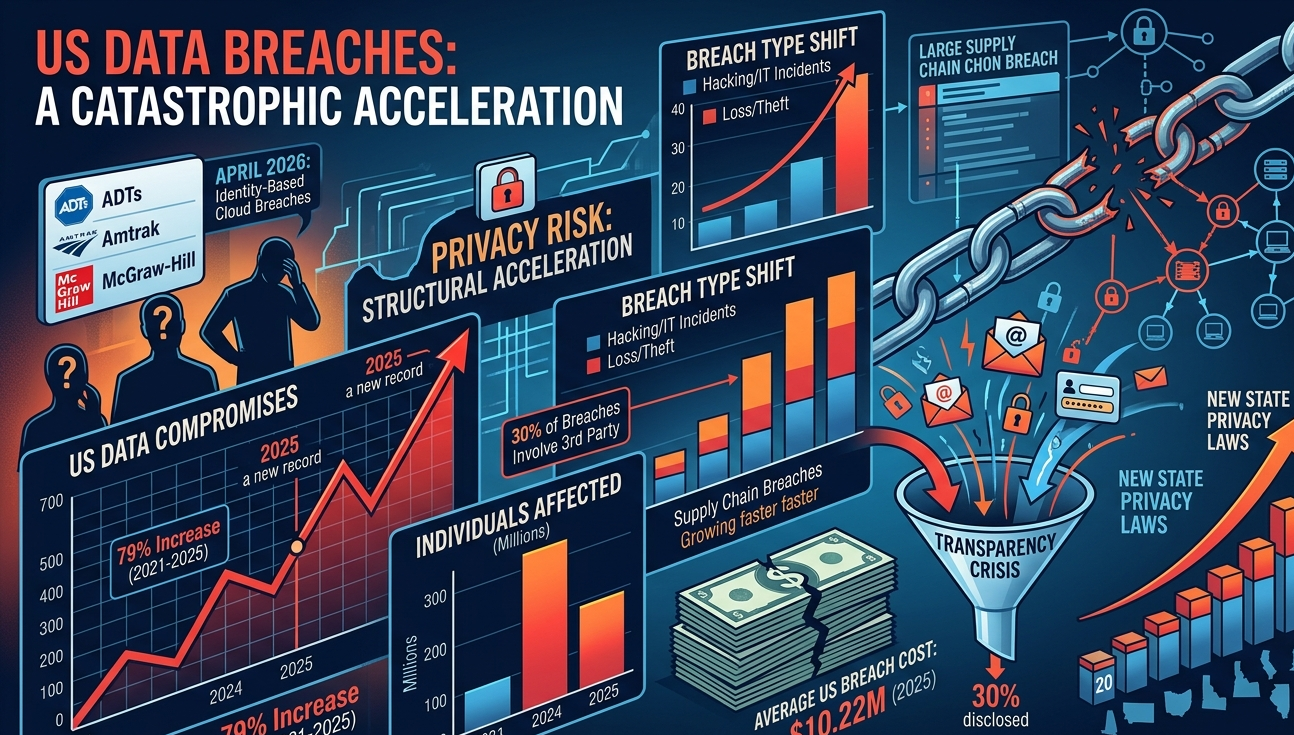
Five Years of US Privacy Breach Data Tell a Story Security Leaders Cannot Ignore
In April 2026 alone, the ShinyHunters extortion group breached ADT (5.5 million customers), Amtrak (2.1 million ...
-1.png)
Mean Time to Exploit Has Gone Negative. Security Strategy Has to Change.
Mandiant's M-Trends 2026 report puts estimated mean time to exploit at negative seven days. That number should reset ...
.png)
When AI Billing Breaks Trust: What the Claude Code Backlash Says About AI Governance
When AI Billing Breaks Trust: Lessons from the Claude Code Backlash AI adoption is accelerating, but trust is still ...

From Army Ranger to Ethical Hacker: What Cybersecurity Can Learn from the Battlefield
Cybersecurity doesn’t start with tools, it starts with mindset. In this episode featuring Aaron Colclough, we get a ...

When Elite Cyber Teams Can't Crack Web Security
HTB's 2025 benchmark tested 796 security teams. Only 21% passed web security challenges. The Security Illusion Security ...

The Invisible Threat: Business Logic Flaws in Modern Applications and Why Scanners Miss Them
In today's security landscape, some of the most dangerous vulnerabilities aren't flagged by automated scanners at all. ...

Suzu Labs Acquires Emulated Criminals
Bridging the gap between theory and the threat reality, Suzu Labs is proud to announce the acquisition of Emulated ...

The Wall Around Claude 4.7 Does Not Extend to Dread
Anthropic released Claude Opus 4.7 on April 16, 2026 with automated cybersecurity safeguards and a Cyber Verification ...

The Engagement Ratchet: How YouTube, Instagram, and Amazon Trained Users to Accept Less Control
Earlier this year, YouTube began rolling out a row of algorithmically recommended videos at the top of the ...

The AI Revolution: How Jobs Will Change by 2030
Host Phillip Wylie sits down with Nicolas Chaillan to discuss the sobering reality of AI replacement, the critical need ...

The Rosie Protocol: Is AI-Driven Personalized Medicine Finally Here?
In late 2024, Sydney tech entrepreneur Paul Conyngham was told his rescue dog, Rosie, had months to live. She was ...

From Analog Hacks to Agentic AI: The Evolution of Offensive Security with Denis Calderone
The world of cybersecurity has undergone a massive transformation in just a few decades. In this episode of Simply ...
.png)
While TSA Made Headlines, CISA Went Dark
The Department of Homeland Security has been partially shut down for over 45 days. In that time, 460 TSA officers have ...

The Purple Team Advantage: Bridging the Gap Between Hacking and Management with Chris Marks
In cybersecurity, we often operate in silos. The red team breaks things, the blue team fixes them, and management ...

Claude Mythos and the Cybersecurity Risk That Was Already Here
On March 26, Anthropic confirmed the existence of Claude Mythos, an unreleased AI model described internally as "a step ...

BPFdoor in Telecom Networks: The FCC Is Securing the Edge, but China's Hackers Are Already Past It
Rapid7's research reveals China-linked kernel implants deep inside telecom signaling infrastructure. Here's what ...

Securing the AI Frontier: Suzu Labs Sweeps 4 Global InfoSec Awards 2026
We are incredibly proud to announce a monumental achievement. At this year’s Global InfoSec Awards 2026, hosted by ...

From Cockpits to Code: Josh Mason on Bridging the Gap Between Military and Cybersecurity
In the world of cybersecurity, we often talk about "gatekeeping" or the "skills gap," but rarely do we find individuals ...

Simply Offensive Podcast: The Future of Pentesting: AI, Automation, and Better Reporting with Dan DeCloss
The Future of Pentesting: AI, Automation, and Better Reporting with Dan DeCloss In this episode of Simply Offensive, ...

From Silence to Strike: Tracking Iran's Cyber Escalation in Real Time
On March 12, medical technology giant Stryker confirmed a cyberattack that wiped devices across 79 countries. The ...

Internal Analysis: Even Realities G2 Smart Glasses Security & Privacy Investigation
Executive Summary Even Realities markets its G2 smart glasses as the privacy-conscious alternative to Meta Ray-Bans. ...

The Company Reviewing Your Meta Glasses Footage Has a Security Problem
Last week, Swedish journalists revealed that Meta sends video footage from Meta Ray-Ban smart glasses to human data ...
.png)
The Death of the CTF: How Agentic AI Is Reshaping Competitive Hacking
View White Paper Abstract: Agentic AI systems are compressing competitive hacking timelines faster than the ...

Simply Offensive Podcast: AI Killed the CTF Star with Jacob Krell
In this thought-provoking episode of Simply Offensive, host Philip Wylie sits down with Jacob Krell, a penetration ...

Anthropic and Claude: 2026 AI Powerhouse
In early 2026, the image of Anthropic as a cautious, safety-oriented "research lab" has effectively been replaced by ...

Simply Offensive Podcast: Navigating AI's Challenges in Problem Solving with Darius Houle
In this episode of Simply Offensive, host Philip Wylie welcomes Darius Houle, an Application Security (AppSec) and ...

Simply Offensive Podcast: Exploring the World of Hardware Hacking with Matt Brown
In the latest episode of the Simply Offensive podcast, host Philip Wylie sat down with Matt Brown, a renowned hardware ...

Simply Offensive Podcast: Exploring AI Vulnerabilities in Cybersecurity with Mike Bell of Suzu Labs
In today’s rapidly evolving technological landscape, the convergence of artificial intelligence (AI) and cybersecurity ...

Simply Offensive Podcast: Emulated Cyber Crime with Dahvid Schloss
Beyond the Pentest: Why Adversarial Emulation is the Future of Defensive Training Many organizations operate under the ...

Under Armour Breach: What The Forum Data Actually Shows
On January 18, 2026, the Everest ransomware group made good on their threat and released Under Armour customer data to ...

SilentFrame: A Research POC on Post-Exploitation Credential Collection through Browsers
This article is in reference to our newest POC hosted on GitHub here: https://github.com/Emulated-Criminals/SilentFrame ...

Brightspeed Breach: Crimson Collective and the Infostealer Problem
Recently Crimson Collective claimed they breached Brightspeed and grabbed 1 million+ customer records. The list of data ...

When Grid Data Goes Dark Web
Inside a threat actor's critical infrastructure targeting In January 2026, 139 gigabytes of engineering data from a ...

The $150,000 Password
How one threat actor turned stolen credentials into a global breach portfolio Between December 2025 and January 2026, a ...

Seeing Everything, Understanding Nothing
To help you get a head start on making your environment safer and in keeping with the theme of January’s “New Year, New ...

New Year, New Priorities - So, what to fix first?
The most common phrase we hear from our prospects is, “We are overwhelmed, and we aren’t sure what to tackle first.” ...

UnderByte — A Ransomware experiment using Alternate Data Streams (ADS)
Repository purpose: this research was to evaluate the feasiabilty of using Alternate Data Stream (ADS) in staging and ...

.jpg?width=1024&height=1024&name=Homepage%20Banner%20Image%20(1).jpg)