
Army Ranger Turned Professional Hacker with Aaron Colclough
In this episode, Aaron Colclough shares his unique journey from military service to cybersecurity, emphasizing the ...
Suzu Labs
-1.png)
Mandiant's M-Trends 2026 report puts estimated mean time to exploit at negative seven days. That number should reset ...
.png)
When AI Billing Breaks Trust: Lessons from the Claude Code Backlash AI adoption is accelerating, but trust is still ...

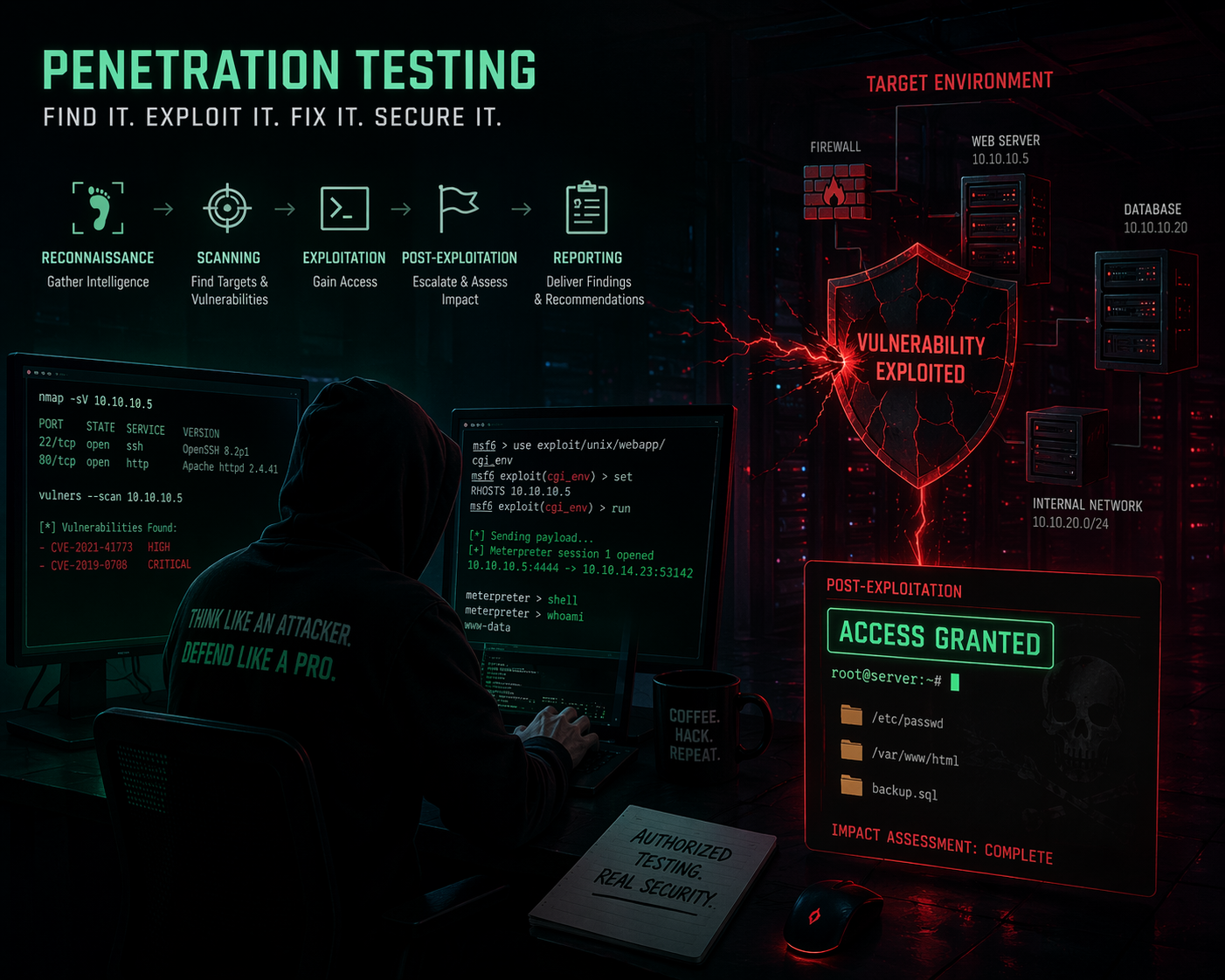
Cybersecurity doesn’t start with tools, it starts with mindset. In this episode featuring Aaron Colclough, we get a ...

HTB's 2025 benchmark tested 796 security teams. Only 21% passed web security challenges. The Security Illusion Security ...

In today's security landscape, some of the most dangerous vulnerabilities aren't flagged by automated scanners at all. ...

Bridging the gap between theory and the threat reality, Suzu Labs is proud to announce the acquisition of Emulated ...

Anthropic released Claude Opus 4.7 on April 16, 2026 with automated cybersecurity safeguards and a Cyber Verification ...

Earlier this year, YouTube began rolling out a row of algorithmically recommended videos at the top of the ...

Host Phillip Wylie sits down with Nicolas Chaillan to discuss the sobering reality of AI replacement, the critical need ...

In late 2024, Sydney tech entrepreneur Paul Conyngham was told his rescue dog, Rosie, had months to live. She was ...

The world of cybersecurity has undergone a massive transformation in just a few decades. In this episode of Simply ...
.png)
The Department of Homeland Security has been partially shut down for over 45 days. In that time, 460 TSA officers have ...

In cybersecurity, we often operate in silos. The red team breaks things, the blue team fixes them, and management ...

On March 26, Anthropic confirmed the existence of Claude Mythos, an unreleased AI model described internally as "a step ...

Rapid7's research reveals China-linked kernel implants deep inside telecom signaling infrastructure. Here's what ...

We are incredibly proud to announce a monumental achievement. At this year’s Global InfoSec Awards 2026, hosted by ...

In the world of cybersecurity, we often talk about "gatekeeping" or the "skills gap," but rarely do we find individuals ...

The Future of Pentesting: AI, Automation, and Better Reporting with Dan DeCloss In this episode of Simply Offensive, ...

On March 12, medical technology giant Stryker confirmed a cyberattack that wiped devices across 79 countries. The ...

Executive Summary Even Realities markets its G2 smart glasses as the privacy-conscious alternative to Meta Ray-Bans. ...

Last week, Swedish journalists revealed that Meta sends video footage from Meta Ray-Ban smart glasses to human data ...
.png)
View White Paper Abstract: Agentic AI systems are compressing competitive hacking timelines faster than the ...

In this thought-provoking episode of Simply Offensive, host Philip Wylie sits down with Jacob Krell, a penetration ...

In early 2026, the image of Anthropic as a cautious, safety-oriented "research lab" has effectively been replaced by ...

In this episode of Simply Offensive, host Philip Wylie welcomes Darius Houle, an Application Security (AppSec) and ...


In this episode of Simply Offensive, host Phillip Wylie sits down with entrepreneur and former U.S. Air Force and Space ...

In this episode of Simply Offensive, host Phillip Wylie sits down with Denis Calderone, Co-Founder and Principal at ...

In this episode of Simply Offensive, host Phillip Wylie sits down with cybersecurity leader Christopher Marks to ...

In this episode, Phillip Wylie interviews cybersecurity expert Josh Mason about his journey from military service to ...

In this episode of Simply Offensive, Phillip Wylie interviews Dan DeCloss, founder of PlexTrack, discussing the ...

In this episode, Phillip Wylie and Jacob Krell discuss the integration of AI in Capture The Flag (CTF) competitions and ...

In this episode, Darius Houle joins the conversation to explore the real-world limitations of AI in problem-solving and ...

In this episode, Phillip Wylie interviews Matt Brown, a hardware hacker and content creator, discussing his journey in ...

In this episode of Simply Offensive, Phillip Wylie interviews Dahvid Schloss, a cybersecurity expert and the emulated ...

In this episode of Simply Offensive, Phillip Wylie and Suzu Labs CEO Mike Bell dive into the intersection of AI and ...

In this episode of Simply Offensive, Phillip Wylie sits down with Len Noe (HaCkEr_213) — the world’s first recognized ...

In this episode of Simply Offensive, Phillip Wylie interviews Shubham Khichi, an offensive security professional and ...

In this episode of Simply Offensive, Phillip Wylie interviews Daniel Lowrie, who shares his extensive background in IT ...

In this episode of Simply Offensive, Phillip Wylie interviews Mike Holcomb, an expert in Operational Technology (OT) ...

In this episode of Simply Offensive, Phillip Wylie interviews Danny Jenkins, CEO and founder of ThreatLocker. Danny ...

In this episode of Simply Offensive, Phillip Wylie is joined by Greg Hatcher and John Stigerwalt from White Knight ...

In this episode of Simply Offensive, Phillip Wylie is joined by Jacob Krell, a cybersecurity professional with a wealth ...

In this episode of Simply Offensive, Phillip Wylie is joined by Corey LeBleu, a cybersecurity professional with over 20 ...

































-optimized.jpg)










.png) WHITEPAPER
WHITEPAPER
This White Paper details how agentic AI is drastically accelerating competitive hacking, with CTF "first blood" times on Hack The Box declining by 16% annually. It argues that hacking competitions are shifting from tests of manual human skill to benchmarks for autonomous AI systems. To preserve the industry's integrity, the author suggests adopting a chess-like model with separate tracks for human and AI-augmented performance.
.png)
This White Paper details how agentic AI is drastically accelerating competitive hacking, with CTF "first blood" times on Hack The Box declining by 16% annually. It argues that hacking competitions are shifting from tests of manual human skill to benchmarks for autonomous AI systems. To preserve the industry's integrity, the author suggests adopting a chess-like model with separate tracks for human and AI-augmented performance.